Arrested, seized, doxed and detained. These are simply among the methods police and prosecutors around the globe took down the most important cyber-crime operations of the yr, even when it meant resorting to new and unconventional eyebrow-raising strategies. From stashing billions of bitcoin below the floorboards to teenage hackers gatecrashing Fortune 500 networks, this yr noticed among the most jaw-dropping breaches — and the highest-profile apprehensions.
As we shut out 2022, we glance again on the cybercriminals we misplaced this yr… to the legislation.
Sanctions and seizures hit the crypto scene
U.S. officers scored some main wins in opposition to crypto-laundering in 2022. Originally of the yr, the Justice Division stated it had seized greater than $3.6 billion value of bitcoins allegedly stolen within the 2016 hack of crypto alternate Bitfinex, and that it had arrested a married couple suspected of laundering the cash.
The couple — Ilya Lichtenstein, 34, and Heather Morgan, 31 — withstand 25 years in jail if convicted on fees of conspiring to launder cash and defrauding the U.S. authorities.
Later within the yr, the Workplace of International Asset Management (OFAC), a watchdog inside the U.S. Treasury tasked with imposing sanctions violations, introduced that it had sanctioned decentralized cryptocurrency mixing service Twister Money for its function in enabling billions of {dollars}’ value of cryptocurrency to be laundered by its platform.
Twister Money, together with different mixers similar to AlphaBay, permits clients to hide the supply of their crypto funds when taking part in a transaction in alternate for a price. It blends probably identifiable or tainted cryptocurrency funds with others to obfuscate the supply and vacation spot of crypto property. Greater than $1.5 billion in proceeds of crime, like ransomware and fraud, has been laundered by Twister Money thus far, consultants estimate.
U.S. doxes alleged Conti ransomware member
In August, the united statesgovernment shared a picture of a suspected Conti ransomware operator generally known as “Goal,” the primary time it has outed a significant ransomware actor. This system additionally supplied as much as $10 million for data resulting in the identification and placement of Goal, together with 4 different alleged Conti members generally known as “Tramp,” “Dandis,” “Professor” and “Reshaev.”
The State Division stated Conti has carried out greater than 1,000 ransomware operations concentrating on U.S. and worldwide important infrastructure. Most lately, the gang infiltrated 27 authorities establishments in Costa Rica and demanded a $20 million ransom.
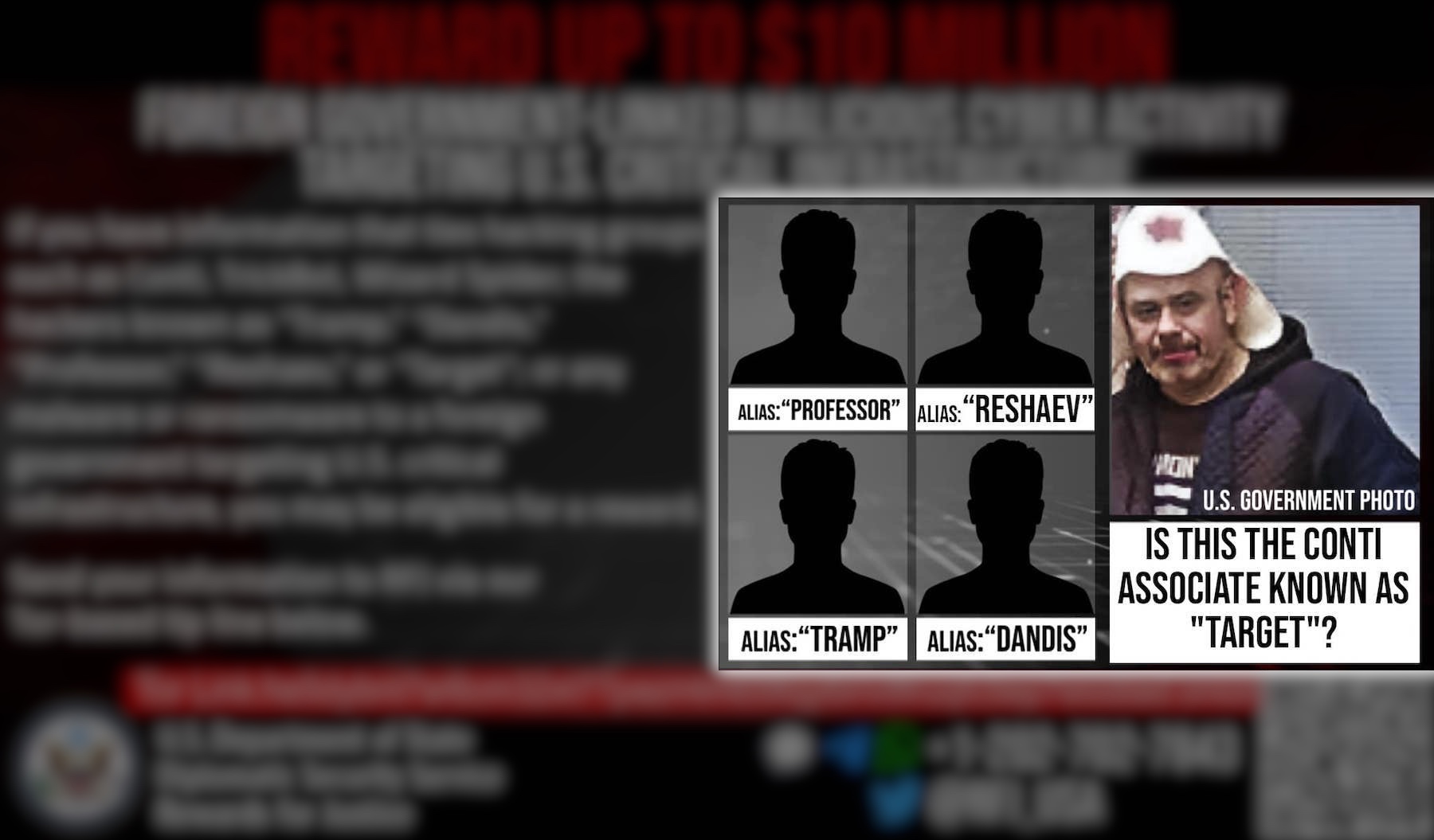
Picture Credit: State Division (handout)
One other gang dealt a devastating hit in 2022 was Netwalker, a ransomware gang that has been linked to quite a few high-profile incidents together with an assault on the College of California San Francisco, which paid a ransom demand of greater than $1 million, and an assault concentrating on cyberthreat startup Cygilant. Between August 2019 and January 2021, ransomware assaults involving NetWalker pulled $46 million in ransom funds, in accordance with cryptocurrency evaluation agency Chainalysis.
In October, Sebastien Vachon-Desjardins, a 34-year-old from Quebec, was sentenced in a Florida courtroom in October after pleading responsible to fees associated to his involvement with NetWalker. Vachon-Desjardins, who labored as an IT advisor for Public Works and Authorities Providers in Canada, was beforehand arrested by Canadian police in January 2021 and sentenced to seven years in jail. Throughout a search of his house, legislation enforcement officers found and seized 719 bitcoin and $790,000 in Canadian forex.
James Zhong, the hacker who stole billions of Silk Street’s bitcoin
In a stunning but anticlimactic conclusion to one of many authorities’s longest working cyber instances, the thriller of the infamous darkish internet medication market Silk Street’s lacking billions was solved. In November, U.S. federal brokers stated it discovered $3.36 billion value of bitcoin that had been stashed in a popcorn can below the lavatory closet floorboards within the house of the hacker practically a decade earlier. Prosecutors introduced fees in opposition to the hacker, a Georgia resident named James Zhong, whose plea settlement with the feds noticed him forfeit the massive cache of cryptocurrency, together with $600,000 in money and different treasured metals.
Considerably confusingly, Zhong is the second hacker to have in the end turned over Silk Street’s stolen billions — albeit at a decrease alternate charge than at the moment. In 2020, a hacker who glided by the alias Particular person X forfeited one other large cache of Silk Street’s bitcoin that that they had stolen years earlier throughout a hacking spree over 2012 and 2013. The Justice Division’s newest forfeiture closed the door on one other billion-dollar thriller, even when the feds saved secret how the funds had been stolen or how they got here to seek out the hacker, lengthy after Silk Street’s founder Ross Ulbricht was jailed.

The partial contents of the popcorn can, containing reminiscence playing cards with billions of cryptocurrency and different treasured metals. Picture Credit: Justice Dept. (handout)
Raccoon Stealer operator charged over mass password theft
U.S. officers in October charged a Ukrainian nationwide over his alleged function within the Raccoon Infostealer malware-as-a-service operation that contaminated thousands and thousands of computer systems worldwide. Mark Sokolovsky, who goes by the web deal with “raccoonstealer,” is accused of getting a significant function as a key administrator of the malware, which prosecutors says was used to steal greater than 50 million distinctive credentials and types of identification from victims around the globe since February 2019.
Sokolovsky is charged with pc fraud, wire fraud, cash laundering and identification theft and faces as much as 20 years in jail if discovered responsible. Sokolovsky is in Amsterdam awaiting extradition to the USA.
Sokolvsky’s arrest led to an uptick in new Mars Stealer campaigns, together with the mass-targeting of Ukraine within the weeks following Russia’s invasion, and a large-scale effort to contaminate victims by malicious adverts. Nonetheless, in November, a safety analysis and hacking startup informed TechCrunch that it had discovered a coding flaw that permits it to lock out operators of the Mars Stealer malware from their very own servers and launch their victims.
Vendor of WhatsApp-hacking tech pleads responsible
Sign jammers, Wi-Fi interception instruments, and WhatsApp hacking instruments. These are among the issues that one Mexican businessman admitted in federal courtroom to promoting for each business and private causes. The Justice Division accused Carlos Guerrero of, amongst different issues, arranging the sale of hacking instruments to Mexican politicians, and utilizing different tools he bought to intercept the telephone calls of a U.S. rival. It goes to point out that it’s not simply nation states and governments with highly effective telephone spying expertise at their disposal.
Lapsus$ rounded up as soon as, twice
The Lapsus$ gang rose to notoriety in 2022. The information extortion group, which first emerged a yr earlier, shortly claimed numerous high-profile victims, together with Okta, Microsoft, Nvidia and Samsung.
Whereas the gang as soon as appeared invincible, numerous its members had been arrested in March this yr. In an announcement given to TechCrunch on the time, Metropolis of London Police confirmed that seven folks between the ages of 16 and 21 had been arrested in reference to Lapsus$.
Information of the arrests got here simply hours after a Bloomberg report revealed a teen primarily based in Oxfordshire, U.Ok. is suspected of being the mastermind of the Lapsus$ group. Researchers investigating the gang’s current hacks stated they believed the 16-year-old, who makes use of the web moniker “White” or “Breachbase,” was a number one determine in Lapsus$, and Bloomberg was capable of monitor down the suspected hacker after his private data was revealed on-line by rival hackers. Weeks later, U.Ok. police stated that they had charged two of the youngsters with a number of cyber offenses.
SSNDOB, a market for stolen Social Safety numbers, is not any extra
U.S. officers in June introduced the takedown of SSNDOB, a infamous market used for buying and selling the non-public data — together with Social Safety numbers, or SSNs — of thousands and thousands of People.
The landmark operation was carried out by the FBI, IRS and the DOJ, with assist from the Cyprus Police, and noticed authorities seize 4 domains internet hosting the SSNDOB market.
SSNDOB listed the non-public data for roughly 24 million people in the USA, together with names, dates of beginning, SSNs and bank card numbers and generated greater than $19 million in income, in accordance with prosecutors. Chainalysis reported individually that {the marketplace} has obtained practically $22 million value of bitcoin throughout over 100,000 transactions since April 2015, although {the marketplace} is believed to have been energetic for a number of years previous to its eventual seizure.
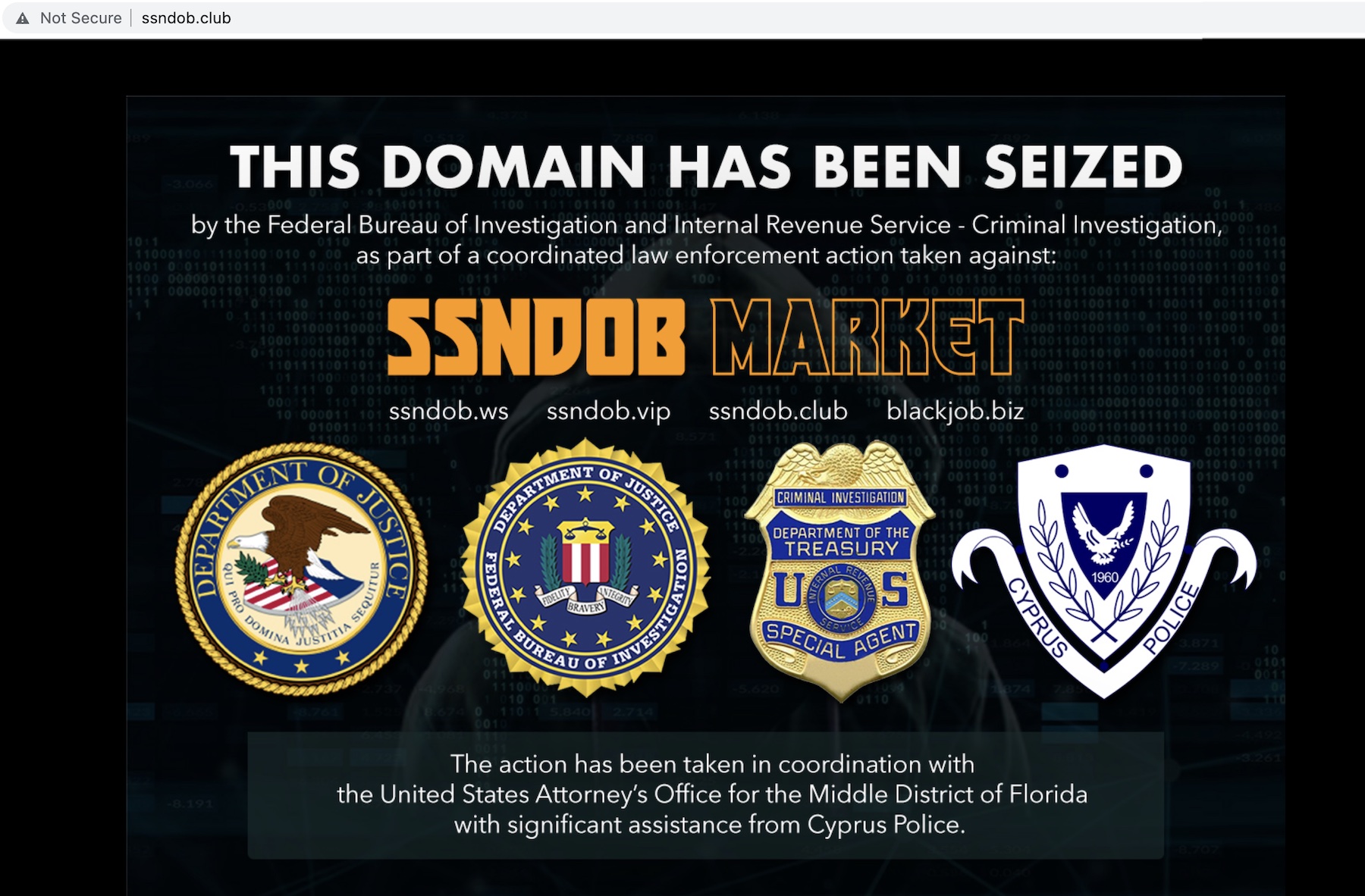
The FBI’s seizure discover on SSNDOB, shortly after the location was taken down by federal authorities. Picture Credit: TechCrunch (screenshot)
Ex-Amazon engineer convicted of Capital One knowledge heist
Additionally in June, Paige Thompson, a former engineer in Amazon’s cloud division, was convicted of a breach that compromised the non-public and monetary data of 100 million CapitalOne clients in 2019. The breach was one of many largest financial institution heists in U.S. historical past, which included the theft of credit score scores, limits and balances, and in addition affected 1,000,000 Canadians. Thompson was accused of utilizing her information as an Amazon software program engineer to breach CapitalOne’s on-line cloud storage, hosted on Amazon’s servers, and compromising the cloud storage of a number of different firms, together with Vodafone, Ford, and Ohio’s state motorized vehicle company. Prosecutors stated the previous Amazon engineer was “one unhealthy day away from sharing the information she stole.” As such, Thompson was sentenced to time served, permitting her to keep away from jail.
A significant REvil operator was extradited to the USA
With a $10 million bounty on their heads after a brazen ransomware assault on Kaseya that unfold to a whole lot of its downstream clients, it was solely a matter of time earlier than the REvil ransomware group’s luck would run out. That’s what occurred with Yaroslav Vasinskyi, a 22-year-old Ukrainian nationwide, who was arrested in Poland in October and later arraigned and extradited to Dallas, Texas to face accusations of pc hacking and fraud by the use of his alleged involvement with REvil. Vasinskyi is one among two different alleged REvil members charged by U.S. prosecutors in relation to the assault on Kaseya. It was solely after the FBI recovered the decryption key that victims had been capable of acquire entry again to their encrypted information.
U.Ok. arrest youngsters linked to Uber and GTA hacks
In September, police in London confirmed {that a} 17-year-old teenager suspected of involvement in high-profile breaches at ride-hailing big Uber and Rockstar Video games had been charged with a number of counts of pc misuse and breaches of bail.
These hacks had been two of essentially the most high-profile of 2022. Uber, which stated it believed a hacker affiliated with Lapsus$ was liable for the assault, was pressured to take a number of of its inside instruments offline whereas it expelled the hacker from its community. Shortly earlier than Uber’s Slack system was taken offline, Uber staff obtained a message that learn, “I announce I’m a hacker and Uber has suffered an information breach.” The hacker additionally reportedly stated that Uber drivers ought to obtain increased pay.
Within the case of Rockstar Video games, the attacker — who additionally goes by the alias “TeaPot” — claimed to have gained entry to Rockstar Video games’ inside messages on Slack and early code for an unannounced Grand Theft Auto sequel by having access to an worker’s login credentials.






